
The Encrypt backup feature in iTunes locks and encodes your information. In this short How To video, Director of Training, Rich Frawley shows investigators how to remove the known iTunes backup..
Go to News article
Investigators can now scan all available Mac computers (including macs with T2 or M1 chips) with all types of encryption and virtual drives by running a remote agent that communicates with the..
Go to News article
Smartphone Triage is becoming more and more important with the exponential increase in the number of devices and explosion of digital data. Mobile device forensic examiners can use smartphone triage..
Go to News article
ADF Solutions mobile phone forensic software makes it easier to quickly collect digital evidence from smartphones and tablets with the Digital Forensic screenshot feature in Mobile Device..
Go to News article
Regular Expressions - (also known as "regex") are special strings representing a pattern to be matched in a search operation and they can be particularly useful in mobile and computer forensics..
Go to News article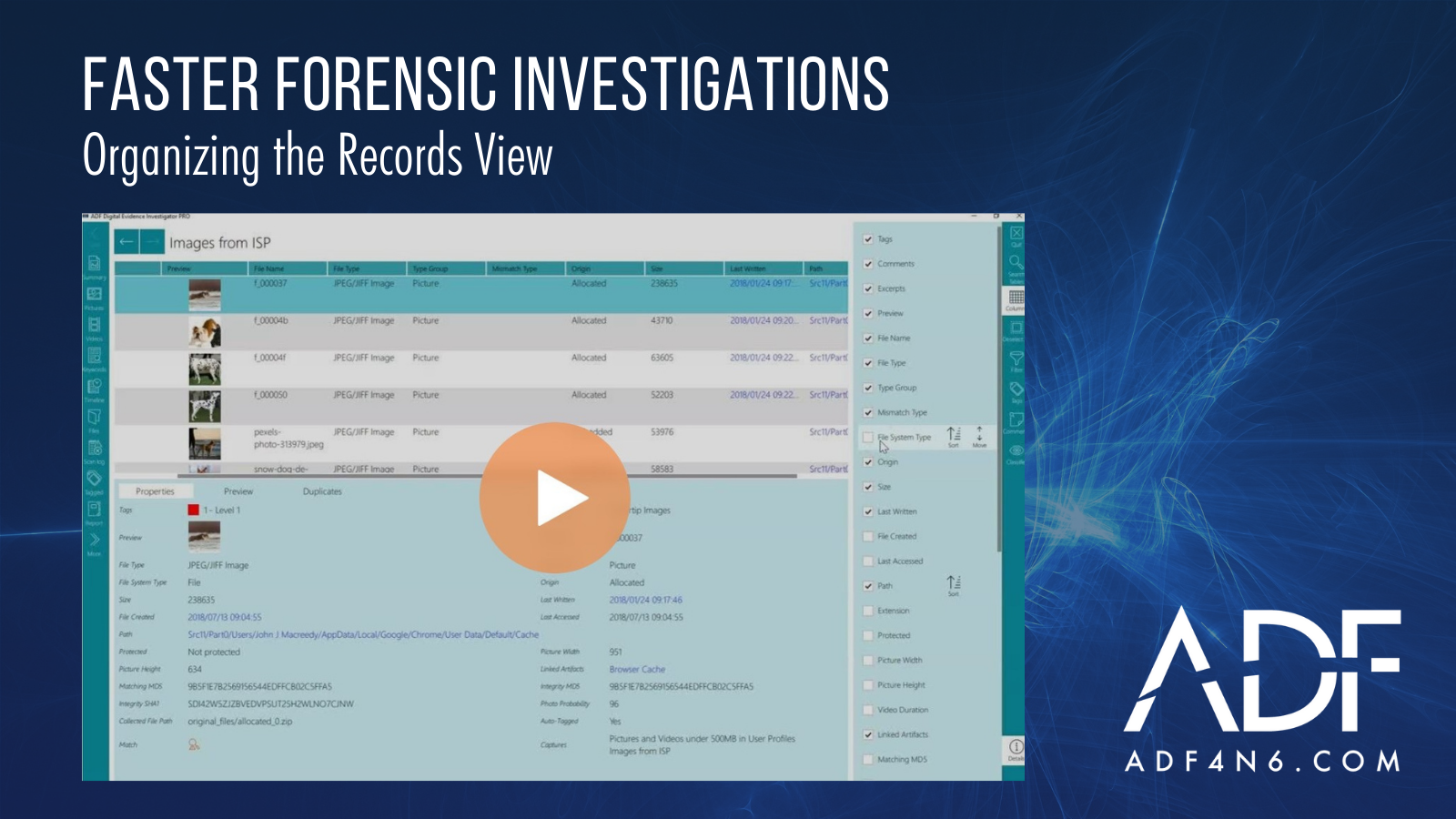
ADF digital forensic software is known for rapid file and artifact collection but we're also widely respected for our seamless user interface. No matter whether you are using Mobile Device..
Go to News articleCopyright 2025 ADF Solutions, Inc. All Rights reserved.