In this short digital forensic How To video, Digital Forensic Specialist, Rich Frawley, walks you through the best settings for Mobile Device Investigator®. Learn how to choose the best Search Profile Capture selection and how to decipher which captures will get you the information you need for your investigation with our mobile phone forensic software.
When setting up ADF Search Profiles for the first time its sometimes difficult to resist picking everything to see what you'll get. If that's your tendency, we've already given you the best comprehensive option with the Search Profile named Mobile Devices - General Profiling and Mobile Devices - Child Exploitation.
However, if you are looking for specific information, you can also create your own Custom Search Profile. In this video you'll learn what you need to do to create a solid profile that will get you the digital evidence you expect.
Get Started with ADF Settings in MDI
Go to Setup Scans → New Profile
ADF Capture Groups are to the left and the captures for each group are on the right hand side.
With Applications highlighted you can see the available captures on the right.
How to know which captures will work for your investigation?
As a refresher, Artifact Captures recover specific records or information e.g. browsing history records or user account information. Users cannot create or edit Artifact Captures. File Captures recover files matching certain criteria such as file properties, inclusion of keywords or matching hash values. File Captures are supplied with the program and can also be user created.
If you look at the Installed Applications Capture, MDI denotes it as an artifact capture by showing the icon of the Operating System it will collect records from, selecting this artifact capture will collect artifacts from Windows, OSx, Android, or iOS.
If you look at the Messages Capture, MDI denotes the icons for the applications it will parse from (Kik, Telegram, Viber, etc.) and know that this will recover artifacts from the specific applications - but what OS will it recover artifacts from? With mobile devices it comes down to what is available in the Advanced Logical Acquisition. Take for example Android, which leaves it to the app vendor, whether or not the app data is stored in the backup, so it is important to know that for certain apps you will not be able to recover data. 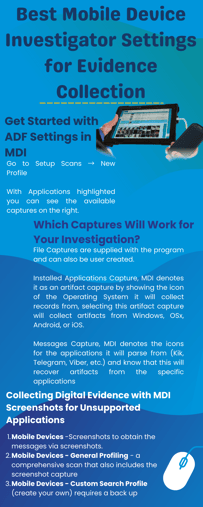
Using MDI to Collect Messages: Example Use Case
A popular app right now is Kik, in the video you can take a closer look at this.
Communications → Messages → Expand
You'll see all the messaging apps that are supported - but which OS will be supported? You can refer to the ADF technical specifications documents to get more information on MDI, system requirements and specific supported apps. Each supported application lists all the artifacts that the ADF Captures can collect from as well as Operating Systems, smartphone apps, and computer applications (for ADF computer forensics). The versions listed are the ones that were tested but the Captures probably support older and newer versions as well.
In the video example, Kik is broken down into two categories - Messages and Contacts. You'll see the app versions tested and the OS that information can be parsed from. So even though Android is listed, it was tested and determined that data was available in earlier OS extractions from an Android, and in the example, Rich demonstrates extracting evidence from Android 9.
When creating a Search Profile you'll want to select Communication categories so MDI will look for and parse any supported and available apps, however, you now know that Kik records will most likely not be available in the Advanced Logical Backup.
Having this knowledge you can now select the screenshots capture located in the Capture Groups Applications.
Collecting Digital Evidence with MDI Screenshots for Unsupported Applications
In a scenario where an investigator or examiner has an Android device and Kik is the messaging Application you are interested in you'll have checked the Technical specifications and determined that Kik may not get parsed. In this scenario you have several options:
- Mobile Devices - Screenshots to obtain the messages via screenshots. This option does not require the phone to be backed up (See How To use MDI Screenshots video)
- Mobile Devices - General Profiling - a comprehensive scan that also includes the screenshot capture - requires back up (See How to video)
- Mobile Devices - Custom Search Profile (create your own) requires a back up (See How To create Custom Search Profiles video)
What to Know and Remember About Mobile Evidence Extraction
For this purpose we supply a warning after a mobile extraction: "This application performed an advanced logical acquisition of an Android/iOS device. Artifacts may exist that are not collected during this acquisition and will not be presented in the scan results."
In other words, an app may be on the phone but it may not be possible to capture results. Be knowledgeable and remember to:
- Confirm the existence of the application (Installed Application / Visual)
- Confirm ability to acquire/parse through technical Specifications
- Collect Screenshots and/or create backup and parse


