 Document and Media Exploitation (DOMEX) requirements cover a wide range of objectives, goals, and users. This includes digital forensics, rapid assessment (or forensic triage) of digital data and devices, collection of data on devices to bagging and tagging of devices.
Document and Media Exploitation (DOMEX) requirements cover a wide range of objectives, goals, and users. This includes digital forensics, rapid assessment (or forensic triage) of digital data and devices, collection of data on devices to bagging and tagging of devices.
DOMEX also supports several mission objectives including biometric identification and other sensitive site exploitation and intelligence gathering objectives. Users of DOMEX tools range from non-technical operators to technically trained forensic examiners.
DOMEX Levels
- Level 1: Tactical exploitation at point of capture
- Level 2: Unit organic or theater level exploitation (FOB)
- Level 3: National level exploitation (e.g. CONUS, IC agencies)
The following cover the options available for analyzing digital devices at Levels 1 and 2:
- Triage – automated process aimed at capturing actionable intelligence as quickly as possible (time constrained)
- Automated Forensics – automated process aimed at capturing actionable intelligence with a broader scope (less time constrained than triage)
- Full Manual Forensic Analysis – highly technical and manual process aimed at capturing actionable intelligence with full scope
Key DOMEX Factors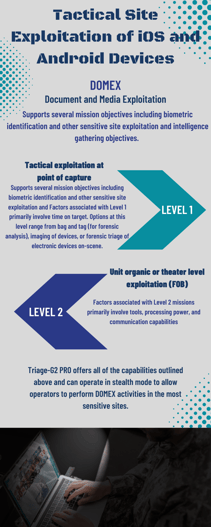
The key factors for organizations to consider when equipping operators are:
- Technical Role of Operators when encountering digital devices
- Risk/Reward Analysis of each approach
- Efficient/Intelligent collection methodologies
Level 1 Factors
Factors associated with Level 1 primarily involve time on target. Options at this level range from bag and tag (for forensic analysis), imaging of devices, or forensic triage of electronic devices on-scene. There are both risks and rewards for each approach and the options deployed are most often associated with the situational risk factors.
Level 2 Factors
Factors associated with Level 2 missions primarily involve tools, processing power, and communication capabilities. When sending data back for analysis at level 3, data transfer speeds can prohibit sending large amounts of data. Gathering as much intelligence as possible from devices can be critical, especially when time is of the essence. With terabyte storage capacities today, full drive acquisitions are inefficient due to dead space, system files, etc. Restricting the amount of data across networks is critical.
The Best DOMEX Solution - Triage-G2 PRO
Designed for non-technical operators, Triage-G2 PRO will rapidly scan, extract, and analyze critical intelligence from iOS/Android smartphones, tablets, computers (Mac, Windows, Linux) and digital devices. The software is typically deployed in the field for reconnaissance on a small, rugged USB key but it can also be licensed to a computer or in a full biometric identity kit.

