 Tactical site exploitation requirements cover a wide range of objectives, goals, and users. This includes digital forensics, rapid assessment (or triage) of digital data and devices, collection of data on devices to bagging and tagging of devices. Users range from non-technical operators to technically trained forensic examiners. The most common devices that operators encounter today are mobile computing devices, mainly iOS and Android phones and tablets.
Tactical site exploitation requirements cover a wide range of objectives, goals, and users. This includes digital forensics, rapid assessment (or triage) of digital data and devices, collection of data on devices to bagging and tagging of devices. Users range from non-technical operators to technically trained forensic examiners. The most common devices that operators encounter today are mobile computing devices, mainly iOS and Android phones and tablets.
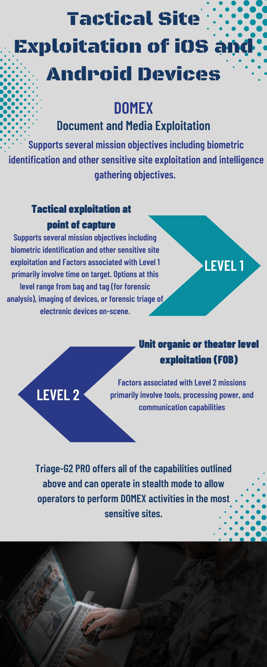
- Level 1: Tactical exploitation at the point of capture
- Level 2: Unit organic or theater-level exploitation (FOB)
- Level 3: National level exploitation (e.g. CONUS, IC agencies)
Level 1: Tactical Exploitation at the Point of Capture
Factors associated with Level 1 missions primarily involve time on target. Here are two use cases that highlight this:
- An operator is attached to a unit moving through an area and comes across civilians of unknown allegiance. The operator then conducts a quick rip of their cell phones in order to understand their identity the best way they can. Given that time is limited, the operator must extract as much information as possible from the devices.
- When working with sources, operators need to understand who they are working with, who they are aligned with, who they know, what they have been doing, whether they are trustworthy or not. The operator may want to interview a source using the source’s mobile phone memory as a verified source of truth. Any intelligence collected off the mobile device in a short amount of time can assist with conducting an effective interview.
Level 2: Theater Level Exploitation (FOB)
Factors associated with Level 2 missions primarily involve tools, processing power, and communication capabilities. Here's an example:
An operator has secured 5 mobile devices and 3 SD cards and has come back to base. The devices have several media files and also a large number of emails and documents in 4 foreign languages. The devices will be sent to a forensic lab for further analysis, but they would like to extract as much intelligence as possible prior to this.
In both cases, the operators require immediate or quick access to the devices. Additionally, if the devices contain languages other than English, operators will need a gisting capability to process data.
The ideal capabilities for these scenarios will be:
- Immediate access to the mobile device data after connection (no initial backup process)
- The process uses only standard transfer protocols that cannot be blocked by the device manufacturers and don’t require hacking (rooting/jail-breaking) of devices
- Take screenshots of applications when their data is inaccessible with other methods
- Scan mobile devices and storage media (flash drives, SD cards, etc.) with the same application and User Interface
- Simple and easy-to-use extraction experience designed for an austere environment
- Powerful post-scan tasks including:
- Classify photos and videos in visual groups
- Extract entities from documents and translate those from over 230 foreign languages
- Text indexing for fast keyword searches
- Hardware agnostic software that can be installed on existing operator tablets
Triage-G2 PRO offers all of the capabilities outlined above and can operate in stealth mode to allow operators to perform DOMEX activities in the most sensitive sites. Non-technical operators can perform sensitive site exploitation with a simple 2-step process and leverage the tightly integrated Rosoka Add-On to translate messages and analyze text and documents in over 230 languages into English with entity extraction and gisting capabilities.

