Intelligence gathering is a discipline that's on a different playing field than your typical law enforcement search warrant or forensic triage examination. ADF's Triage-G2 and Triage-G2 PRO enable military field operatives to rapidly collect and exploit captured equipment, media and documents in theaters of operation around the world and reduce time on target for:
- Counterterrorism
- Force protection
- Information warfare
- National security needs
In this 2 minute How To video you'll learn how to use Stealth Mode in Triage-G2 or Triage-G2 PRO.
Whether it is a covert tactical media exploitation exercise, or a clandestine military operation where the need for stealth DOMEX is required then ADF Triage tools are just the tool to satisfy your sensitive site exploitation requirements. 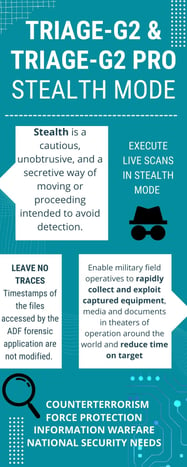
Stealth is defined as a cautious, unobtrusive, and a secretive way of moving or proceeding intended to avoid detection. Live scans executed with Triage-G2 can operate in “Stealth Mode”. In this mode, Triage-G2 makes it difficult to locate traces on the target computer as using Stealth Mode during your scan will help conceal your presence.
When utilizing Triage G2 in the field and a Live Windows computer is encountered, the ability to exploit that computer and not leave any traces is essential. During a live scan, the timestamps of the files accessed by the ADF forensic application are not modified.
Once your scan has started TG2, provides fast and reliable intelligence gathering followed up with powerful Entity Extraction and multilingual text analysis and translation to English in 230+ languages. Gisting to English with the Rosoka Add-on included in ADF's tactical site exploitation products.
Triage-G2 is the leading digital forensic triage software typically deployed in Biometric Kits for Sensitive Site Exploitation. Operators are trained in Triage-G2 by ADF Solutions digital forensic specialists and certified trainers or by the National Forensic Science Technology Center (NFSTC) which provides exploitation training as an intensive interactive course to prepare operators to gather Intel on-site.
Want to learn more? Watch Intro to Triage-G2 with Rosoaka Entity Extraction and Gisting (Live On-Demand)


